How to Create a Public/Private Key Pair
- Start the key generation program. myLocalHost% ssh-keygen Generating public/private rsa key pair.
- Enter the path to the file that will hold the key.
- Enter a passphrase for using your key.
- Re-enter the passphrase to confirm it.
- Check the results.
- Copy the public key and append the key to the $HOME/.
Today, the RSA is the most widely used public-key algorithm for SSH key. But compared to Ed25519, it's slower and even considered not safe if it's generated with the key smaller than 2048-bit length. The Ed25519 public-key is compact. It's also fast to perform batch signature verification with Ed25519.
Checking for existing SSH keys
- Open .
- Enter ls -al ~/.ssh to see if existing SSH keys are present: $ ls -al ~/.ssh # Lists the files in your .ssh directory, if they exist.
- Check the directory listing to see if you already have a public SSH key. By default, the filenames of the public keys are one of the following: id_rsa.pub. id_ecdsa.pub.
Press Clone or download and press Use SSH in the panel that appears. The panel will change to Clone with SSH with the updated link. Copy the link by pressing the Copy To Clipboard icon. Open Git Bash and navigate to the directory in which you want to clone the repository.
ssh-add adds private key identities (from your ~/. ssh directory) to the authentication agent ( ssh-agent ), so that the ssh agent can take care of the authentication for you, and you don't have type in passwords at the terminal.
I suggest that you follow those steps:
- Step 1: Check for existing SSH keys. $> ls -al ~/.ssh.
- Step 2: Generate a new SSH key. $> ssh-keygen -t rsa -b 4096 -C "yourEmail"
- Step 3.1: Add the SSH key to your GIT account. Get your public key.
- Step 3.2: Force SSH Client To Use Given Private Key.
- Step 4: Clone the project.
How to Generate SSH Key in Windows 10
- Generate an SSH key in Windows 10 with OpenSSH Client. Step 1: Verify if OpenSSH Client is Installed. Step 2: Open Command Prompt. Step 3: Use OpenSSH to Generate an SSH Key Pair.
- Generate SSH Keys Using PuTTY. Step 1: Install PuTTY. Step 2: Run the PuTTY SSH Key Generator.
- Using Your SSH Keys.
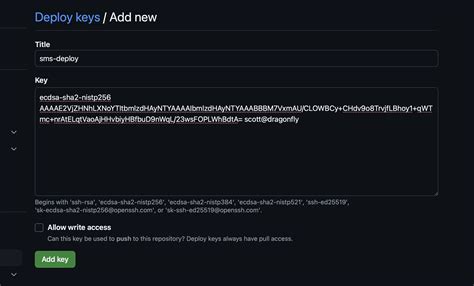
A deploy key is an SSH key that is stored on your server and grants access to a single GitHub repository. They are often used to clone repositories during deploys or continuous integration runs.
In the following steps, we will set up our repository and push code to it:
- Go to the newly created repository.
- Select the URL in the top-right section.
- Go to the folder where you want to check out the project in the terminal.
- Enter the Git clone command, and change the URL to the URL you just copied:
Whenever you will execute a Git command that will communicate with GitLab, it will check the permissions you have against your own user account. One thing to remember is that you can only use one SSH key for one account, as it will be account-bound.
Following this guide, you will be able to create and start using an SSH key. Git is capable of using SSH keys instead of traditional password authentication when pushing or pulling to remote repositories. Modern hosted git solutions like Bitbucket support SSH key authentication.
I am talking about just GitHub and GitLab but you can use the same for any cloud git providers. Many times it happens that when you push to your GitHub repository you have to enter your GitHub password each time.
From your repository, click Settings. In the sidebar, click Deploy Keys, then click Add deploy key. Provide a title, paste in your public key. Select Allow write access if you want this key to have write access to the repository.
Generating a new SSH key
- Open .
- Paste the text below, substituting in your GitHub email address. $ ssh-keygen -t ed25519 -C ""
- When you're prompted to "Enter a file in which to save the key," press Enter. This accepts the default file location.
- At the prompt, type a secure passphrase.
Do not store API keys or signing secrets in files inside your application's source tree. If you store API keys or any other private information in files, keep the files outside your application's source tree to help ensure your keys or other private information do not end up in your source code control system.
A public/private key RSA pair is generated, which is stored in the Android device's keystore and protected usually by the device PIN. An AES-based symmetric key is also generated, which is used to encrypt and decrypt the secrets.
One possibility would be to hard code the
secret key into the source code of the program itself.
Here is the scenario:
- I need to encrypt some data (file)
- This data will be read by a program (say written in C/C++).
- Both the program binary and encrypted data will be accesible to some arbitrary user.
API keys provide project authorizationBy identifying the calling project, you can use API keys to associate usage information with that project. API keys allow the Extensible Service Proxy (ESP) to reject calls from projects that haven't been granted access or enabled in the API.